
6 – Middlemen, Inside Access and Manipulation –
A fractional voting framework is treacherous because it can be scaled to run across multiple jurisdictions very quickly. False results precisely mimic known patterns to appear plausible. In the demonstration we performed, Smith’s one-size-fits-all utility showed that a person without any programming skills at all could seize control of election results in several counties at a time, even though each county had different precincts, races, and candidates. Vendors and well-placed middlemen can alter results in multiple states. GEMS’ unique design offers both product and service.
We have discussed two ways to weight a race:
a. By candidate (assign percent to candidate)
b. By voter (assign weight to each voter)
Weight by candidate allows the greatest breadth of execution.
What is needed to weight by candidate?
1. A set of desired percentages;
2. An inside manipulation utility;
3. A trifling moment of access to the GEMS election database.
1. Creating desired percentages
Such information is gathered for various reasons, such as targeting voters for advertising and get-out-the-vote efforts. Percentages can be shaved or enhanced, then cut and pasted into a fractional voting utility.
When testing ‘fraction magic’ Smith searched out prior precinct results to mimic plausible results. When he explained to Harris that such research is necessary, Harris recalled a questionably timed results file, found on one of Shelby County’s computers. It contained precinct results for Shep Wilbun – a candidate who had exposed a slush fund and subsequently was hit with successive voting system irregularities when he tried to regain his seat. For some reason a 2006 precinct results report for Wilbun’s prior election was created shortly before Wilbun’s 2010 election. Certainly not a claim of tampering, but precisely the type of strategic planning document one would need in order to target Wilbun’s election.
– Russell Michaels, producer of Hacking Democracy
For 15 years, GEMS has been described as flawed and full of security holes. Smith may be one of the first researchers to express respect for GEMS’ sophistication. Researchers have pointed out that with GEMS, votes can be flipped to reverse candidate totals. Smith counters that in a real election such an approach would appear almost cartoonish, with Black Democratic strongholds voting for White Republicans and vice versa. At the very least, simple vote-flipping is reckless and imprecise. On one level, GEMS enables crude manipulations by local users, but on a deeper level it offers refined and scaled-up control to persons who are provided with a specific kind of utility.
Smith first imagined the necessary program structure to create a product capable of selling election results. He then examined GEMS to rule out the existence of such a framework. To his surprise, the more he tried to rule it out, the more the framework was ruled in. Smith further concluded that it wasn’t even necessary to build an exploit. Instead he built a tool to work within the already existing design. Smith struggles with the terms “hack” and “exploit” because what he designed was already facilitated in GEMS.
One would not expect to find such an architecture in a voting system. Indeed, though GEMS violates U.S. Voluntary Voting System Technical Guidelines in broad strokes 1 the guidelines never address fractional votes.
GEMS is more complex than we have described. It involves an elaborate maze of normalization with generic column names. Relationship mappings are omitted. Overlapping nomenclature uses the same identifier to represent different data sources. Queries are generic and the output is the product of all included tables. Information displayed in queries is often replicated in several variations with cryptic or missing notations. Internal and shrouded data structures and reports are hidden in the executable.
In short, to sell election results, either someone needs to hand the utility to you or you have to don hip boots, a caver’s headlamp and a helmet and submerge yourself into GEMS, where, after you slog through the mess, you will find exactly what you need already waiting for you. The fractional vote program is best described as an inside tool.
We now examine who has opportunity to tunnel through elections if given the necessary tool.
3. A trifling moment of access
We looked at the issue of employees, temporary workers, vendors and middlemen gaining access to central tabulation systems (Bear in mind that opportunity does not equal execution.) We looked at four ways to access the database:
1. Direct access to GEMS server or database
2. Substitution of a copy of database
3. Inserting script through removable media
4. Remote access to database
Direct access to GEMS server
There are approximately 3,000 different counties in the U.S., each with employees who have some level of access to the central tabulator. The following testimony provides a picture of the various people who access the GEMS server directly in Shelby County, Tennessee:
ADMINISTRATOR OF ELECTIONS RICHARD HOLDEN 2:
Q. Okay. Who all at the Election Commission has access to the GEMS server?
A. Myself, the deputy administrator of elections and the information systems personnel.
Q. And by the information systems personnel, does that include the temporary employees in that section?
A. There are times when the temporary employees have physical access to that room.
COMPUTER SYSTEMS ANALYST DENNIS BOYCE 3
Q: How many temps do you have under your purview at the time?
A: At the time now or …
Q: At the time of the August election.
A. I had six.
…
Q. Who else on your staff?
A. I had a resource. Ruth Ann Phelps
Q. … would anybody else have been there with her?
A. That’s hard to say.
Q. Who all had access to the tabulating room for the August election period?
A. The tabulation room was the IS department.
Q. Okay.
A. And the administrator has the codes too.
Q. Do your temps also have that access?
A. Yes.
Q. And for what reason would anybody be in the tabulating room other than maintenance of the computer?
A. We have a switch and routers in that room as well.
Q. Okay.
A. So that would be a reason. And our GIS computer is in there too.
A. … Most of — that’s hard to say exactly who was in there going in and out. As I’ve said before, that’s a tabulation room and it has our routers and switches in there so my staff has access to that room all the time. I can’t give you have a number of who.
* * * * *
The above testimony indicates that a number of different people may find themselves in a position to access to the GEMS computer. It is not necessary to have a password to the GEMS program in order to do fraction magic. Any person who enters the tabulator room while the computer is on has the opportunity alter one location’s election.
Now we move to those with opportunity to affect multiple locations.
Middlemen: The Curious Case of William Doyle
Arizona election integrity activist John Brakey went to Santa Cruz County, Arizona to evaluate its election procedures. Because a local corruption prosecution had produced a high level of tension, a new Nogales mayoral candidate had asked Brakey to size up potential for election fraud.
In locations with a culture of corruption, elections represent a special risk. Elections produce transfer of power, and along with it, transfer of computer records, files, bank accounts, and sphere of influence.
Brakey began by issuing a small set of public records requests to Santa Cruz County elections administrator Melinda Meek. She refused to give up the legally required public records, so Brakey sued for compliance. While on the witness stand Meek claimed that she programmed the database herself.
Official court reporter’s transcript of the testimony of Melinda Meek, Clerk of the Board and Elections Director for Santa Cruz County4:
Q. Okay. And I guess just for the Court’s benefit, what was being requested was an electronic copy of the contract with the vendor who programs the central county election computer and the ACULO [sic] memory card, and you’re saying that does not exist?
A. It doesn’t exist because I do that myself, it’s done in house.
The above testimony can be viewed at 7:15 minutes into this YouTube video: https://www.youtube.com/watch?v=Tx80l2WPZoc
But at 19:17 minutes into the video she also says:
“I receive a database, and it’s programmed into the GEMS system.”
From whom does Meek “receive the database?” After obtaining Meek’s e-mails and the GEMS audit log, Brakey learned that instead of programming GEMS herself, Meek had been subcontracting it out to a private jobber working from his home, a gentleman by the name of William Doyle.
From e-mails Brakey obtained through public records, he learned that Doyle’s process was to e-mail Meek the GEMS database in one e-mail with its password in a second email.
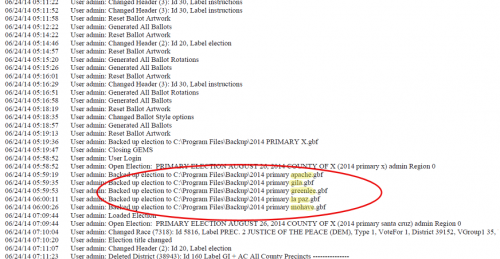
Doyle prepares GEMS databases, then loads them into county computers through a phone modem (the same modem that receives the election results). Brakey obtained copies of the GEMS audit log used in Santa Cruz County.
As you can see below, Doyle not only created the GEMS database for Santa Cruz, but for several other counties as well. His process was to create all the federal and statewide ballot contests which are shared by several counties, then partition out the database into one for each county.
Because Meek seemed unwilling to disclose Doyle’s involvement, and because Brakey became curious about the idea that a single individual working out of his home could gain direct access GEMS databases in several counties at once, he issued records requests all over Arizona for information pertaining to Doyle. He discovered that at one point, Doyle handled election data for 13 of Arizona’s 15 counties, including both GEMS databases and those for another vendor, ES&S. Doyle’s total invoices summed up to over $2 million per federal election cycle.
Doyle, doing business under the name “Election Operations Services” would prepare the GEMS database, then e-mail it to election officials, as testified to in court by a Gila County Division of Elections Director Dixie Mundy5
Q: Who, again, programs the computer for Gila County?
A: The consultant that creates the database for us, for our ballot layout, is Election Operations Services.
Q: Election Operations —
A: Election Operations Services is our consultant. That does our ballot layout for us.
Q: And is that a private company?
A: Yes it is.
Q: And where is that company headquartered?
A: In Glendale, Arizona.
Q: Do you know how many employees they have?
A: I’m not sure how many employees they have, no.
Q: Yes. Ah, what do you know about the company?
A: I know that Mr. Doyle, Bill Doyle, who is the owner of the company, he’s been the consultant for Gila County for well over 16 years. Before I became Elections Director. Mr. Doyle, originally I believe, or prior to this, worked for Maricopa County Elections.
Q: And you say there’s, I forgot — how many people in that company?
A: I don’t know how many employees.
Q: Okay. And do you know who actually works on the program, putting together the ballot for Gila County?
A: I don’t know necessarily the exact employee that would manually do that.
Q: Do you know whether this private company programs elections or sets up the ballots for other counties in Arizona?
A: I believe they do.
Q: Do you know how many counties the election services company and Bill Doyle’s company, prepares the software for?
A: No I do not.
…
Q: Do you give Bill Doyle and executable version of GEMS, do you give him a copy of your GEMS software?
A: No.
Q: Does he have his own copy?
A: I believe he does, yes, but I don’t know what Bill has exactly. I’m assuming he must have something to create our ballot but I can’t say for sure what he has.
…
Q: When Bill Doyle, or one of his employees, brings back the database to use in the election, you actually don’t know what might be in that code that he brings back, do you? Or do you know?
A: What do you mean by what’s in the code?
Q: Well, what form does Mr. Doyle bring this stuff back to you in?
A: I can explain what we receive from Bill Doyle.
Q: Sure.
A: We receive the ballot layout for each of our voting precincts. We print that, we do approve. We also recieve actual ballots so we can create our test.
Q: Okay. So his computer telephones your computer and sends it?
A: Yes.
A single Gila County contract with Doyle authorized $225,000:
“Services are required in order to conduct elections in Gila County. Services provided include consulting and technical assistance for each election; ballot layout, translation, preparation, and printing; elections database programming; creation, printing, and mailing of sample ballots.” 6
In a contract between Yavapai County and O’Neill Printing, William Doyle is identified as their “Elections Liason,” described as providing services to over 100 jurisdictions, including “programming for tally systems and conversion of voter files for mailing company.” 7
Mohave County shows 17 purchases from Doyle for a total of $891,952.61.
A Cochise County election procedure worksheet instructs local election workers to notify Doyle when they upload results8.

Many counterparts to William Doyle
Further research by Harris indicates that several counterparts to William Doyle are at work in other states. Contracts with election vendors often contain a clause authorizing subcontractors, who may or may not be named.
Frank Kaplan, whose name appears on some of the original e-mails pertaining to weighted fractionalized elections in GEMS, now works out of his home in Albuquerque, New Mexico and has been paid for independent election services for Colorado locations9. Kaplan sometimes does business under the name Automated Ballot Concepts, and Automated Election Concepts. Documents from Fort Bend County, Texas and Boulder County, Colorado list Kaplan as Election Services Manager for a larger firm called Integrated Voting Solutions.
Another individual, John Elder out of Lake Stevens, Washington shows up as an independent election consultant10. Oddly, his services are only found when you drill down into a Web site for Showcase Management Group, listed as “Music Production Consultants” in business directories. Elder reportedly acted as an intermediary between Fresno, California and the Integrated Ballot Solutions firm while Victor Salazar was Fresno Registrar of Voters. 11.
A third contractor, Steve Knecht, doing business as Waypoint Election Services12, provides an e-mail with Ballot Concepts, which is Kaplan’s consulting business name.
E-mails and court testimony show that the above individuals (Elder, Knecht, and Kaplan) were knowledgeable about the insertion of the fractional weighted elections in GEMS. All three have been working as middlemen handling election data.
Another election intermediary named Bob Comyn, apparently associated with Kaplan’s consulting outfit, describes the work as follows:
“Design, development and maintenance of ballot processing system using Microsoft Access, .NET, C#, and SQL Server. Ballot Concepts is an intermediary between several Counties in Colorado and California and two large printing firms. We provide value-added services to the Counties.” 13
A contract obtained by Harris for a man by the name of John Paulsen, working out of his home in Castle Rock Colorado, shows that he was given access to interface with tabulators of all makes and models in the state to prepare results. 14

Invoices show that a small firm called Casto & Harris programmed the ES&S data for most of West Virginia15.
A man named Joe Bolton, working out of his home, programmed the Microvote system for Kentucky counties while they were in use. Here is an excerpt from Harris’s interview with Bolton16. , who did state firmly “I don’t do nothin’ like that.”:
Q: Okay. Well you’ve been doing this for 35 years, has anyone ever asked you to do something that made you uncomfortable?
A: Oh, absolutely, get it all the time, I get that all the time you know.
Q: You’re kidding me!
A: “Could you rig this machine?” And I don’t know whether it’s a conspiracy or a joke, you know, “Could you rig these machines for me Joe? How much would it cost me?” I’ve heard that for 35 years.
Now, most of Kentucky voting systems are programmed by Harp Enterprises, an independent contractor out of Lexington.
An outfit called “Election Magic” handles results reporting for several Michigan counties17. Though its technology sounds curiously outdated (advertising support for Windows ’95), it shows services through the 2016 primary for several locations. It seems unlikely that such an outfit would provide sophisticated election database programming, and perhaps it doesn’t. But then again, election data programming is offered by equally unlikely-sounding “Showcase Management” music production group.
Governmental Business Services (GBS) advertises that it does “election programming & coding, custom election software apps, voter registration systems, Election Day support, ballot printing, and voting equipment sales & service”. According to its Web site it handles three Indiana counties and 16 counties in Illinois.18
In the first eight states she examined, Harris compiled a list of over 100 independent election contractors. Weeding out who gets the contracts and what they actually do is an area for further research.
About election contractors:
1. The amount of inside access granted to election consultants and contractors can be vast, while also not clearly delineated.
2. Payments to contractors may or may not be traceable. When a large contractor hires a subcontractor, expenditures leave public view.
3. An examination of county and municipal invoices indicates that a number of small jobbers take on assignments to handle key portions of election management. Sometimes the identity of even formal bidders is unclear. For example, a bidder list for Adams County, Colorado elections includes a vendor listed simply by the name “SM” with phone: “(123) 123 – 1234” zip code “12345”.
The state of Ohio outsourced its entire 2004 presidential election results to a partisan Internet company in Chattanooga, Tennessee, which also handled Republican National Committee work and hosted Republican strategist Karl Rove’s personal e-mails.
A company called SOE software interfaces directly with tabulation systems in over 1,000 U.S. locations, including the entire states of North Carolina, South Carolina, and Georgia.
In fact, after reviewing documents going back to 1985, it is clear that the U.S. ecosystem for election administration is far more complex than most people realize.19
This tapestry of home-based specialty jobbers and middlemen evolved for the simple reason that election officials rarely possess the skills to program and manage their own election technology. Particularly at the municipal and small county level, it is not possible for clerks to conduct their own elections without outside help. Because elections are seasonal, outside election assistance is supplied by specialized freelancers and individual consultants.
Substitution of election databases:
One way to perform fraction magic is to use a copy of the election database, give it the same file name, and overwrite the real election data.
In Pima County, Arizona, it was revealed during litigation that a technician was making copies of the GEMS election database and taking it home overnight, then loading it back onto the official computer in the morning. 20
Multiple copies of the GEMS database should not be floating around during live elections, except as official backup copies, which are passworded and documented in the audit log. When we obtained file directory listings of several computers in the Shelby County elections office, we found live GEMS election databases on four different computers. A “live” GEMS database, in contrast to a backup database, is one with file suffix “.mdb”. Backup GEMS databases have suffix “.gbf”.
DEPOSITION OF SHELBY COUNTY ELECTION OPERATIONS MANAGER ALBERT HOLMES 21
Q. How many GEMS servers are there at the Election Commission Operation Center?
A. Two.
Q. Are there GEM servers at the downtown —
A. — I understand there’s one.
Q. Okay. I was going to say the downtown Election Commission Office. Let me finish.
A. Yes.
Q. Do you know who has access to the GEMS tabulators or the GEMS servers?
A. Not to the one at the main office downtown. I imagine he only has access. The other is in the absentee room.
* * * * *
The above testimony describes three computers containing GEMS. Holmes stated that he also has the program on his own computer and that he can access it from his home. We also found GEMS files on a computer they referred to as the “EPIC server,” which also contained voter lists and electronic poll books. File metadata showed that GEMS files were being shared between various computers. It was unclear which computer was producing the results being distributed to the public. These findings demonstrate that copies of live election databases are produced; that they are sometimes kept in multiple locations, and they are sometimes transferred from computer to computer.
Insertion of removable media:
Shelby County logs from 2006 show that encrypted information of some sort was being inserted on USB sticks. Removable media can be used to replace or alter election data, but it is also used for legitimate purposes, such as transferring results from GEMS (though those files are not encrypted).
Surveillance video in Saguache County, Colorado, taken with an ES&S M650 tabulator, shows an unusual sequence of events. First, it is reported that the election administrator, who was running for her own position in the election, lost the election. Then, she sits down with the voting system technician and berates him so aggressively that he reaches for a box of tissue and cries. Then, the technician surreptitiously locks the door and inserts a zip disk into the ES&S M650 tabulator. Next, the elections administrator announced that she has, after all, won the election. 22
Remote access
Perhaps the greatest access of all goes to the big boys, the four major vendors for election equipment in the world (ES&S, Dominion, Smartmatic, Hart Intercivic). The following excerpt, taken from the deposition of Shelby County Election technician Dennis Boyce, 23 demonstrates that vendors are sometimes provided with remote desktop access during elections. The transcript below refers to remote access being granted to ES&S during Election Day, after Early Voting but before Poll voting had finished:
Q. Okay. And what did Mr. Underwood instruct you to do?
A. Well, Mr. Underwood looked at the data and we had a remote session with WebX and he looked at the data and looked around. We told him what happened and we told him that we needed to resolve the issue. And he looked at the data and they did their little deal or whatever they did to correct it and told us to reconfigure the data again. They kind of reset stuff.
Q. So they could remote into your machines?
A. Our secure remote. Our WebX.
Q. So, what exactly did they do remotely?
A. Well, when they remoted in they reviewed the EPB data, the poll data, and examined it. They ran some scripts against it. And that reset the flags on the records. And once they reset the flags on the records, then they kicked off the scripts again to populate the fields and gave us the new poll data. They said now you can disburse this.
Q. Let me see if I’m understanding this. You speak a different language than I do …
A… What they did was a couple of things. They’d have to speak to this. What I saw them do was run scripts against the database.
* * * * *
Logs from the computer of Dennis Boyce show that “WebEx” access was granted on at least three occasions during running and preparation of the election. The occasion described above pertained to running scripts against the electronic pollbook database. GEMS election databases also resided on the computer which was remotely accessed by Mr. Underwood.
Remote access is sometimes granted for technical support. The above example demonstrates that not only is remote access granted, but that it can be used to run scripts on election data.
* * * * *
To sum it up, direct access to central tabulation data appears to be accessible to multiple persons from each jurisdiction, and there are over 3,000 jurisdictions. Access is also granted to voting system vendors for support services, and to a number of middlemen who have access to multiple jurisdictions, and whose role is often unclear and also undisclosed to the public.
* * * * *
Next:
Part 7 (coming): Whodunnit http://blackboxvoting.org/fraction-magic-7
Previous:
Part 5: Masters of the Universe http://blackboxvoting.org/fraction-magic-5
All:
Part 1: Votes are being counted as fractions instead of as whole numbers http://blackboxvoting.org/fraction-magic-1
Part 2: Context, Background, Deeper, Worse http://blackboxvoting.org/fraction-magic-2
Part 3: Proof of code http://blackboxvoting.org/fraction-magic-3
Part 4: Presidential race in an entire state switched in four seconds http://blackboxvoting.org/fraction-magic-4
Part 5: Masters of the Universe http://blackboxvoting.org/fraction-magic-5
Part 6: Execution capacity – http://blackboxvoting.org/fraction-magic-6
Part 7: Whodunnit – coming – http://blackboxvoting.org/fraction-magic-7
Part 8: Solutions and Mitigations – coming – http://blackboxvoting.org/fraction-magic-8
* * * * *
 Bev Harris is a writer and founder of Black Box Voting. She has researched and written about election transparency and computerized voting systems since 2002. Harris was featured in the Emmy-nominated HBO documentary Hacking Democracy, and is the author of Black Box Voting: Ballot Tampering in the 21st Century, a book purchased by the White House Library and also reportedly found on Osama bin Laden’s bookshelf. Harris’s research has been covered in The New York Times, Vanity Fair, Time Magazine, CNN and several international publications, including the Philippine Daily Inquirer and Agence France Presse. Contact by text or phone 206-335-7747 for media inquiries.
Bev Harris is a writer and founder of Black Box Voting. She has researched and written about election transparency and computerized voting systems since 2002. Harris was featured in the Emmy-nominated HBO documentary Hacking Democracy, and is the author of Black Box Voting: Ballot Tampering in the 21st Century, a book purchased by the White House Library and also reportedly found on Osama bin Laden’s bookshelf. Harris’s research has been covered in The New York Times, Vanity Fair, Time Magazine, CNN and several international publications, including the Philippine Daily Inquirer and Agence France Presse. Contact by text or phone 206-335-7747 for media inquiries.
 Tucson-based John Brakey is Co-founder of AUDIT-AZ, and a Special task force leader for Citizens Oversight for Verifiable Elections. He has engaged in groundbreaking public records investigations, elections observations and election litigation, working with one of the most effective election transparency litigators, Attorney Bill Risner. Brakey has been involved in front-lines election transparency work since 2004.
Tucson-based John Brakey is Co-founder of AUDIT-AZ, and a Special task force leader for Citizens Oversight for Verifiable Elections. He has engaged in groundbreaking public records investigations, elections observations and election litigation, working with one of the most effective election transparency litigators, Attorney Bill Risner. Brakey has been involved in front-lines election transparency work since 2004.
 Bennie Smith is a Memphis-based application developer for an electrical manufacturing company. He is also a political strategist who has developed a micro-targeting application that predicts voter turnout. In August 2014 he was approached by a number of candidates who insisted that their elections had been stolen. He disagreed with the group and offered to look into how the system works. After discovering a number of irregularities, Smith began to research how votes that originate from the same source can change once they get into the GEMS vote tabulation program. Smith’s attention to these anomalies uncovered an extraordinarily high-risk tampering mechanism and ultimately provided a new infrastructure for analyzing questionable election results.
Bennie Smith is a Memphis-based application developer for an electrical manufacturing company. He is also a political strategist who has developed a micro-targeting application that predicts voter turnout. In August 2014 he was approached by a number of candidates who insisted that their elections had been stolen. He disagreed with the group and offered to look into how the system works. After discovering a number of irregularities, Smith began to research how votes that originate from the same source can change once they get into the GEMS vote tabulation program. Smith’s attention to these anomalies uncovered an extraordinarily high-risk tampering mechanism and ultimately provided a new infrastructure for analyzing questionable election results.
* * * * *
- U.S. Voting Systems Standards Volume I – Performance Standards, April 2002; Federal Election Commission. http://www.eac.gov/assets/1/Page/Voting%20System%20Standards%20Volume%20I.pdf
In view of what we now know about the design for fractionalized weighted elections, GEMS violations are egregious. For example:
2.2.1 Security
b. Provide system functions that are executable only in the intended manner and order, and only under the intended conditions.
Requirements for DRE voting machines are not included for central tabulators like GEMS:
2.4.3.3 DRE System Standards
m. Ensure that the votes stored accurately represent the actual votes cast;
n. Prevent modification of the voter’s vote after the ballot is cast.
For central tabulation, alteration of vote data is constrained only to specific instances:
2.5.3.1 g. Prevent data from being altered or destroyed by report generation, or by the transmission of results over telecommunication lines.
The “Fraction Magic” tool is not caused by report generation or data transmission over phone lines.
Section 4.2.7, Comment Conventions, part a (1)-(6) and b. are completely ignored in the GEMS source code.
Section 6, Security Standards, is not followed in GEMS:
6.1 Scope …
– To protect the system from intentional manipulation and fraud, and from malicious mischief;
– To identify fraudulent or erroneous changes to the system;
…the Standards identify several types of risk that must be addressed by a voting system. These include:
– Unauthorized changes to system capabilities for:
– Calculating vote totals consistent with defined ballot formats; and
– Reporting vote totals;
– Changing, or preventing the recording of, a vote;
– Introducing data for a vote not cast by a registered voter;
– Changing calculated vote totals;
Adherence to the standards is supposed to be examined by an independent testing authority (ITA), but testing lab, iBeta passed the system anyway, resulting in a scathing letter from voting system researchers Aaron Burstein and Joseph Lorenzo Hall, along with 12 other signatories (but GEMS is still being used as of 2016):
https://www.verifiedvoting.org/california-top-to-bottom-reviewers-letter-to-the-election-assistance-commission/ ↩ - In The Matter Of: Regina Newman vs. Shelby County Election: Deposition of Richard Holden, Sept. 30, 2010 Vol. I, Pg. 2 ↩
- In The Matter Of: Regina Newman vs. Shelby County Election: Deposition of Dennis Boyce, Sept. 28, 2010, pgs 7-8. ↩
- Superior Court of the State of Arizona in and for the County of Santa Cruz: Americans United for Democracy, Integrity and Transparency in Elections – AUDIT-AZ; John Brakey, et. al vs. Santa Cruz County Board of Supervisors, Melinda Meek, et. al; Official court reporter’s transcript: Excerpt from proceedings, testimony of Melinda Meek.
Video of testimony: https://www.youtube.com/watch?v=Tx80l2WPZoc ↩ - Gila Elections Director Dixie Mundy Cross Examined by Attorney Bill Risner
https://www.youtube.com/watch?v=WiUmGX96KEY ↩ - Executive Summary Form — Professional Service Agreement: Elections Operations Services Contract Number: _1005.103/2-2011
http://agenda.gilacountyaz.gov/docs/2011/REGULAR/20110405_58/390_EOS%20Executive%20Summary%20Form.pdf ↩ - Election services contract between Yavapai County and O’Neill Printing:
http://aq.co.yavapai.az.us/docs/2016/BOS/20160601_608/9167_O’Neil%20Printing%20Contract.pdf ↩ - Ballot Audit worksheet
agenda.cochise.az.gov/docs/2012/SPCL/20120308…/674_BALLOT%20AUDIT.xlsx ↩ - Automated Ballot Concepts: Brokering of Election Ballots and Services
https://www.corporationwiki.com/New-Mexico/Albuquerque/automated-ballot-concepts-llc/108169542.aspx
Automated Ballot Concepts, LLC. The company has one principal.
http://www.bizapedia.com/ca/AUTOMATED-BALLOT-CONCEPTS-LLC.html
Town of Dillon, Town Council Regular Meeting, March 18, 2014
http://www.townofdillon.com/Modules/ShowDocument.aspx?documentid=2836
Summit County Government Warrant Publication List: May, 2015
http://www.co.summit.co.us/ArchiveCenter/ViewFile/Item/1293
Vendor List, El Paso County Colorado
http://adm.elpasoco.com/BudgetAdministration/Budget/Documents/Vendor%20List/Vendor%20List%206-01-16.pdf
Fort Collins, Colorado
Vendors/Payees: Automated Ballot Concepts, LLC
http://www.fcgov.com/openbook/?action=match-vendor&vendor=AUTOMATED+BALLOT+CONCEPTS+LLC&from=NOV-01-2013&to=OCT-30-2015
Fort Bend, Texas County Bid #09-105
https://agendalink.co.fort-bend.tx.us/mindocs/2009/CCTR/20091013_2106/minutes/2099_23e2%20contract.pdf ↩ - John Elder worked for Spectrum Print & Mail, then Global Election Systems, then Diebold Election Systems (same firm, as it went through acquisitions). Then he became an independent elections consultant working out of his home in Lake Stevens. He has often referenced a long-time friend, Eric Kozlowski, who runs Integrated Voting Solutions out of Fresno Calif. Elder’s home address is at one point listed as “Integrated Voting Solutions” in Washington State. http://www.buzzfile.com/business/Integrated-Voting-Solutions-425-322-5575
“Integrated Voting Solutions is located in Lake Stevens, Washington. This organization primarily operates in the Computer Related Consulting Services business.”
Integrated Voting Solutions is listed as an active corporation in Washington State:
Its company number is 603240513. INTEGRATED VOTING SOLUTIONS, INC. was registered on 12.01.2012. The company’s status is listed as Active.
http://www.washingtoncorps.com/corp/173713.html
At some point Elder (through his wife) started Showcase Management Group, listed as “Music Production Consultants” – also with home address. However, the Web site for Showcase Management Group describes only election intermediary services, like programming election databases and various vote-by-mail and political petition software services. See http://showcasemi.com and http://showcasemi.com/services/ ↩ - This was reported in detail to Harris by a well-placed source who was concerned that Elder, convicted of narcotics trafficking in 1992, was doing some sort of programming or services using Fresno County voter databases. Elder had spent four years in prison (1992-1996). Almost immediately upon release from prison he began work in the elections industry ↩
- Waypoint Election Services: See California corporations database; also see LinkedIn profile for Steve Knecht: https://www.linkedin.com/in/steve-knecht-b1597b5 ↩
- LinkedIn profile for Bob Comyn. https://www.linkedin.com/in/bob-comyn-2b32885 ↩
- 2008 Information Technology Services Contract with LEDS, LLC and the state of Colorado http://blackboxvoting.org/docs/ LEDS-contract.pdf; See also: Colorado Corporation Search LEDS LLC identification number: 19991051560 ↩
- Public records obtained by Bev Harris for Fayette County, West Virginia: See: http://blackboxvoting.org/docs/WV-Fayette.pdf ↩
- See Moonshine Elections Part 1 – http://blackboxvoting.org/docs/moonshine1.pdf
Video: https://www.youtube.com/watch?v=tpzahSVY_GM ↩ - Election Magic: http://www.electionmagic.com/ ↩
- According to its Web site, GBS performs election services for Elkhart, Brown, and Parke counties in Indiana; and Boone, Carroll, Cass, Cumberland, Fulton, Greene, Johnson, Knox, Lee, Morgan, Perry, Pike, Scott, Warren, Washington and Whiteside counties in Illinois. https://www.gbsvote.com/ ↩
- Documents contributed to Black Box Voting by Eva Waskell identify election services contractors going back into the 1980s, some of whom were investigated for tampering with punch card computers in West Virginia and Texas. ↩
- See Documentary: Fatally Flawed – watch for Bryan Crane’s testimony about taking GEMS databases home. https://youtu.be/Sfk4wcULA-M ↩
- In The Matter Of: Regina Newman vs. Shelby County Election: Deposition of Albert Holmes September 29, 2010, Pg 34 ↩
- Ballots, lies and videotape; Feb. 2, 2011: Colorado Independent, by Troy Hooper. Includes video clips. http://www.coloradoindependent.com/76759/ballots-lies-and-videotape-in-saguache-county ↩
- In The Matter Of: Regina Newman vs. Shelby County Election: Deposition of Dennis Boyce September 28, 2010, Pg 13-14 ↩

2 Comments